For the longest time, my router/firewall solution has been a Raspberry Pi 3 with a USB network dongle running dnsmasq. While this worked well enough, it didn’t offer much by way of advanced configuration (at least not easily), and the lack of a GUI was often a pain. Plus, I wanted my Raspberry Pi back. So, in this saga, we’ll be taking a look at how to create a virtualized firewall by running pfSense on VMware ESXi.
What We’ll Be Building
I like visual diagrams, so to kind of lay out what we’ll be doing, here’s a crudely MS Paint-ed diagram of how the virtual network will function:
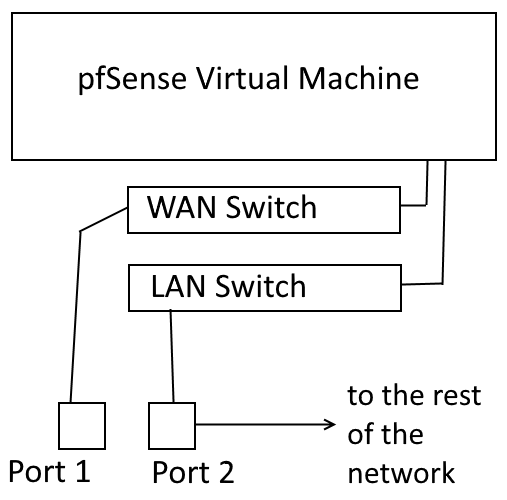 my 3rd grade computer teacher would be proud
my 3rd grade computer teacher would be proud
Step 1: Requirements
So, for this project, you need a couple things. First, you need a server running VMware ESXi 6.x. Importantly, that server should have at least 2 network ports. That will enable us to have a WAN and a LAN port. For this, I’ll be using my Dell PowerEdge R710, which has 4x1GbE ports on the back, and it runs VMware ESXi 6.5.0.
Note: With some finagling, the same result can be achieved with a single NIC using VLANs, as long as your switches/infrastructure support it. This, however, is beyond the scope of this tutorial.
Obviously, you will also need a WAN connection, as well as a switch or device to connect to the LAN port.
Learn from my mistakes: Don’t forget to download pfSense before you start reconfiguring your internet connection…
Step 2: Configuring ESXi & Management Connection
To achieve our virtual firewall, we’re going to create 2 virtual port-groups in ESXi: one for the WAN connection, and one for the LAN connection and add a physical port to each of those groups.
Create The Virtual Switch(es)
We need to add the virtual switch for our LAN connection, then assign it to a physical port. Do this by logging into the ESXi interface and accessing Networking > Virtual Switches > Add standard virtual switch.
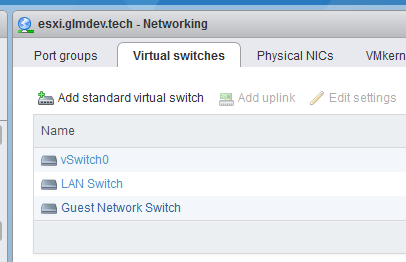 Additional interfaces for the firewall should be added here.
Additional interfaces for the firewall should be added here.
Name the switch something meaningful and assign it a physical port.
For the WAN switch, we’re going to use the built-in “VM Network” switch. If you want any additional network ports for the firewall, add them now.
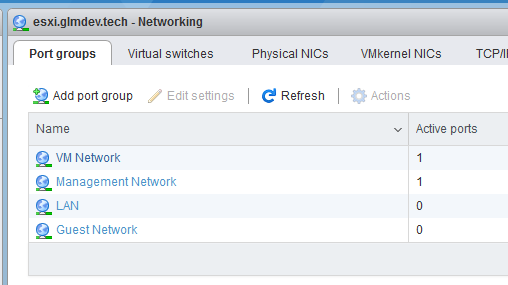
Now, we need to create “port groups” for the new switches. Open the Port Groups tab and create port groups for each of the new switches you added.
The Management Connection
During most of this process, your computer will not have internet access, or DHCP service. This means that, in order to maintain access to the ESXi interface, we need to set static IP addresses on both the ESXi management interface and the computer we’re working from.
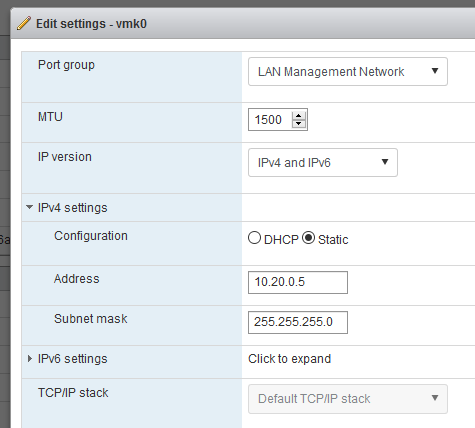
From the networking tab, access VMkernel NICs > vmk0 > Edit Settings > IPv4 settings
Set a static IP address that is within the address space of the new network. (i.e. if the new network is 10.20.0.1– 10.20.0.255, I picked 10.20.0.5)
Save and Apply the settings. Then, open your computer’s network settings and set its static IP to something in the same address space, and set the IP of the ESXi host as the gateway. This will disrupt internet/intranet communications, but it will ensure continual access to the ESXi interface.
Step 3: Installing pfSense
In point of fact, this can really be done with any firewall/router software you want to use (IPFire/OPNsense/routerOS/etc), I just chose pfSense.
Create a new virtual machine, and, for pfSense, select OS family: Other and set the OS to “FreeBSD (64-bit).”
Tab through the wizard until you land on the VM’s configuration page. Here we need to modify a few things.
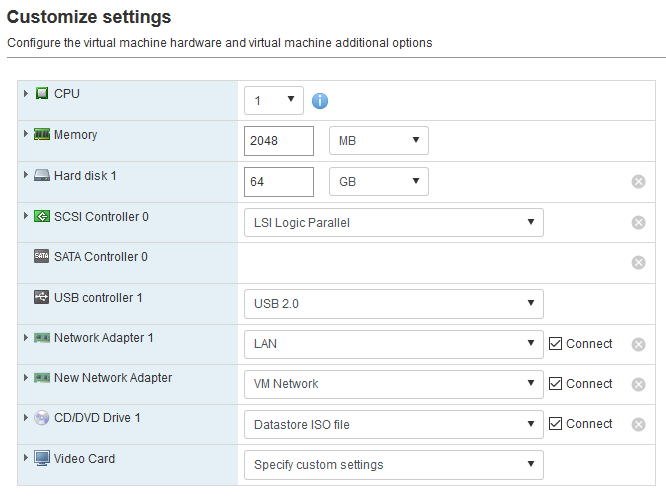
Add an additional Network adapter using the button at the top, and then select the LAN port-group we created earlier. You should have a network adapter with a WAN port-group by default.
Then, in the CD/DVD drive, select the pfSense installer ISO from the datastore. Now you can click create and start the VM.
pfSense Install
The basic installation of the pfSense operating system is nearly identical to installing it on bare-metal. Just click through the installer until the system reboots and you land on the set-up page.
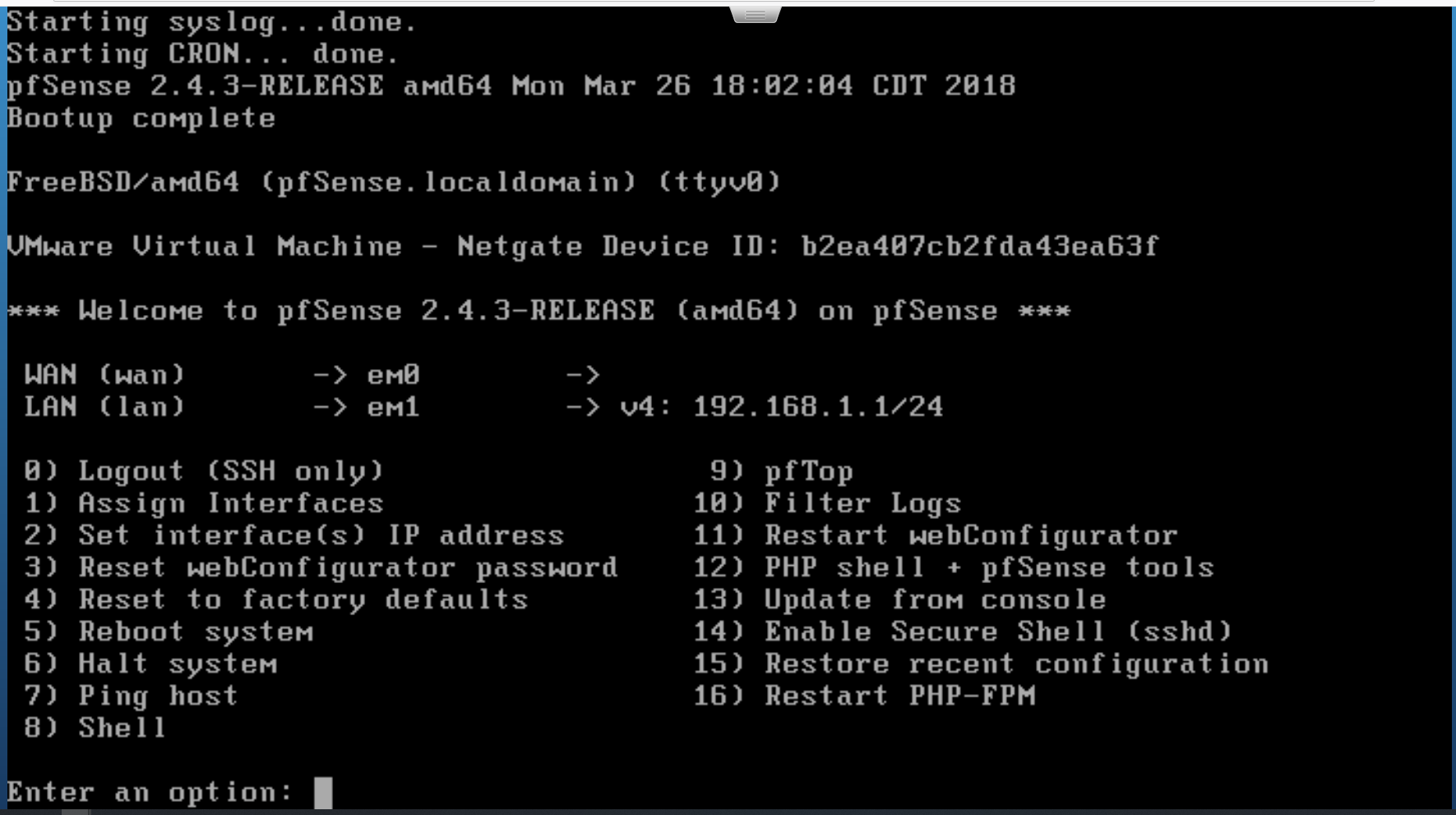 the pfSense setup page
the pfSense setup page
To make things easier on ourselves, we’re going to pre-configure a few things from here before opening the web interface. First, we need to set up the WAN interface. Even though my WAN doesn’t have DHCP, pfSense was able to automatically select which interfaces are supposed to be which.
Select option 2 to Set interface(s) IP address.
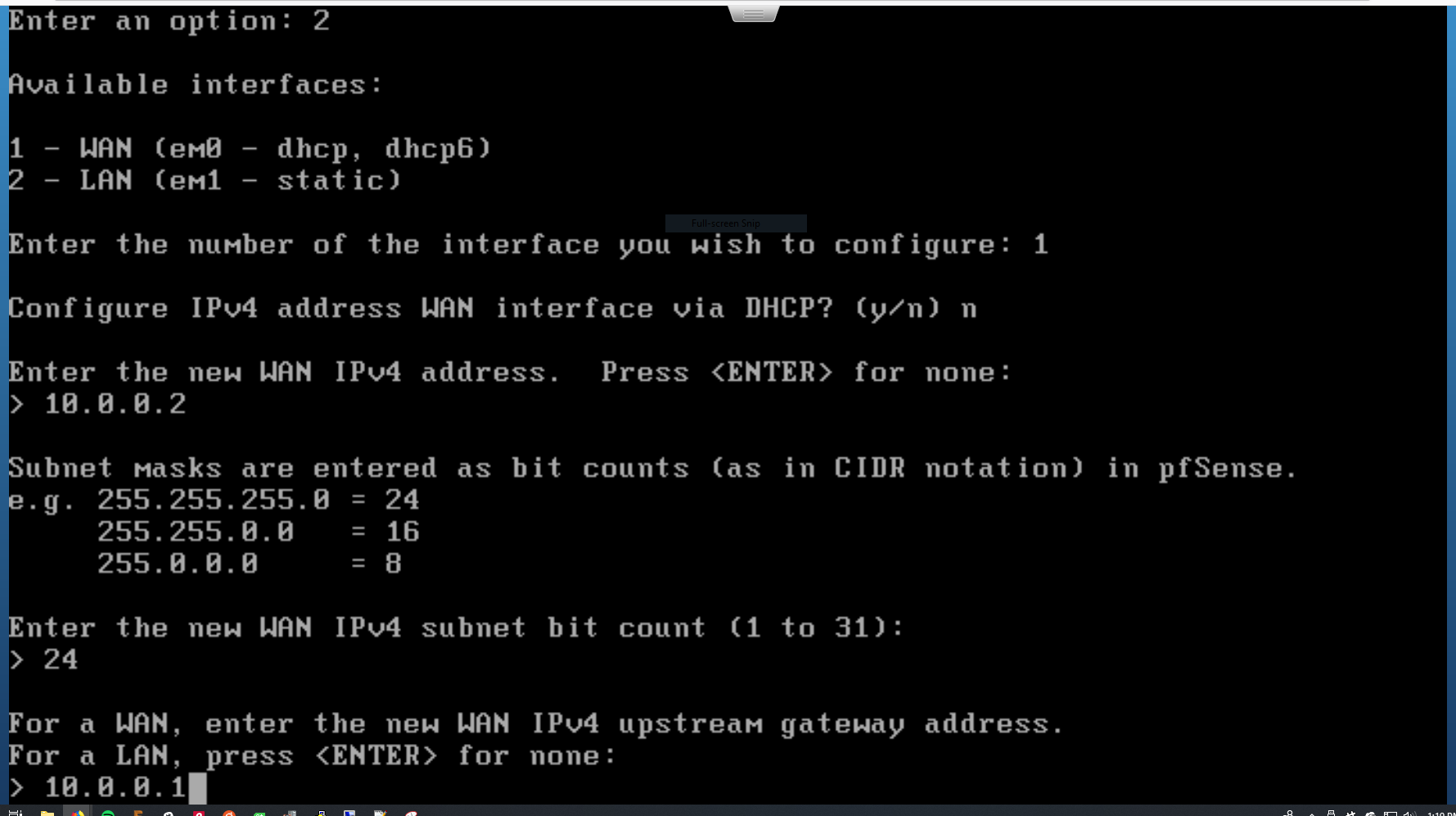 configuring the WAN interface
configuring the WAN interface
This will launch an interactive wizard that will help you configure an interface. Select the WAN interface to configure, then just run through the wizard.
For me, this involved setting the static IP address of the port and pointing it toward my gateway.
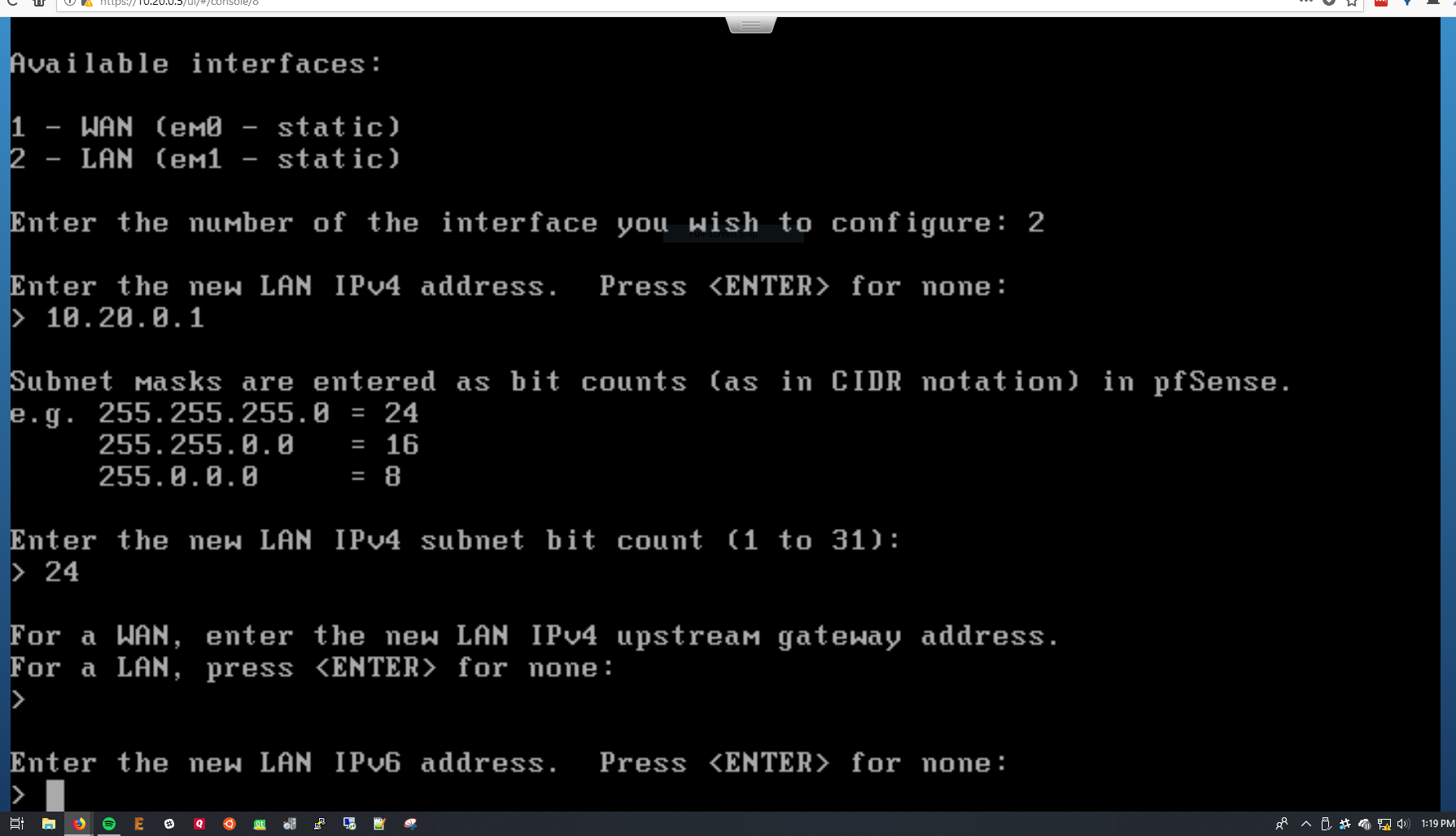 configuring the LAN interface
configuring the LAN interface
Now, we repeat the process for the LAN interface. Here you’ll be prompted to set the static IP again, as well as selecting a DHCP range for pfSense’s LAN port. Make sure this is the same address space as you planned earlier (for me, 10.20.0.X).
Select y to enable the DHCP server, and press enter to save.
Step 4: Moving to the New Network
We now officially have a virtual firewall running, but before we can start using the new network, there are a few configuration things to modify.
The Management Network (reprise)
In order to access our ESXi host from the new network, we need to move the vmk0 management interface over to the LAN switch we created earlier. However, we can’t just add it to the existing LAN port group (ESXi hates that, for some reason), so we’ll create a new port group. Access Networking > Port Groups > New Port Group.
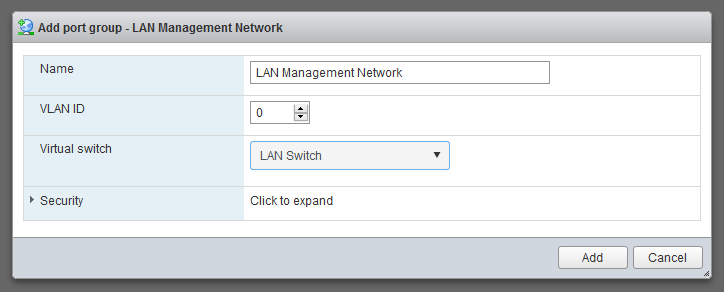
Create a new LAN Management Network port group on the same LAN switch we created earlier.
This will make sure it bridges with the LAN port on the new pfSense VM.
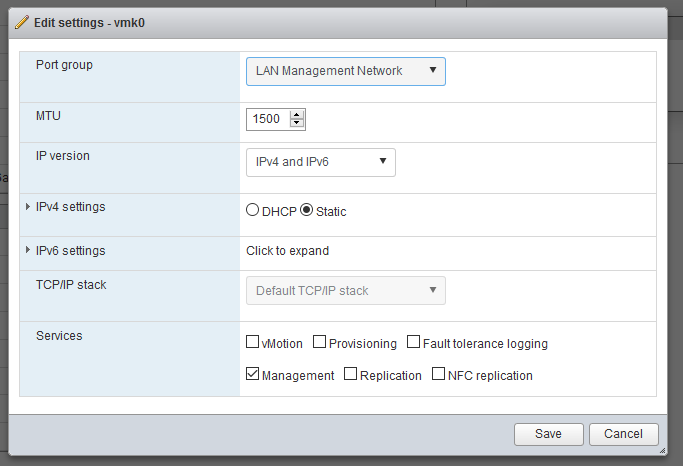
Now, go to Networking > VMkernel NICs > Edit Settings and change the port group to the new LAN Management Network port group we just created.
Note that after you save the settings, you’ll no longer be able to access the ESXi interface. This is normal.
Move It Over!
Now, we can finally start using our new network! Move the connection to the switch (or the rest of your physical network) to the new port on the server that we added to the LAN switch we created at the beginning. This will connect your network to the pfSense LAN interface.
Finally, reset your computer’s IP address back to DHCP so it will pick up an address and DNS from pfSense.
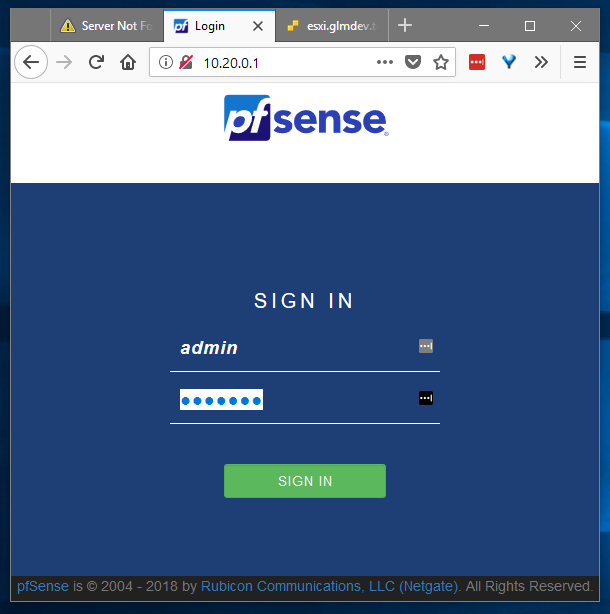
Open up your web browser of choice and navigate to the IP address you assigned to the pfSense LAN interface in Step 3, and voila! You should be presented with the pfSense web interface.
Log in using the default credentials:
admin
pfsense
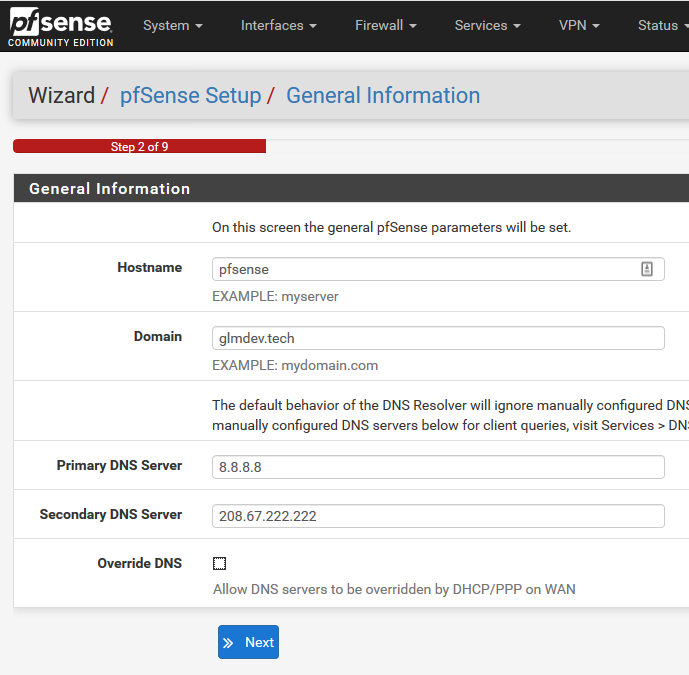
Now it’s just a matter of running through the standard pfSense setup wizard and you’re off to the races!
pfSense will behave exactly like it would if it were installed on a physical box. This means that everything from DNS to VLANs to captive portal will behave normally.
Plus, you should still be able to access the ESXi host. :)
Conclusion
Virtualized networking is a great way to experiment with different firewall software without having your network down for long periods of time. It also lends a lot of flexibility when it comes to customizing network segments.
I hope this guide has been helpful, and if you have any questions, comments, or if you run into any issues, leave a comment down below, and I’ll do my best to help!